Agile methodologies have revolutionized the programming world, providing a flexible and iterative approach to building high-quality applications. By emphasizing collaboration, customer feedback, and continuous improvement, agile practices enable teams to quickly adapt to changing requirements and deliver value in short sprints. Agile methods, such as Scrum and Kanban, promote transparency and accountability, fostering a culture of ownership among team members. The result is software that is not only functional but also meets user needs effectively.
- Agile methodologies prioritize customer feedback, ensuring that the final product aligns with user expectations.
- The iterative nature of agile development allows for continuous improvement and refinement throughout the software lifecycle.
- By breaking down projects into smaller sprints, agile teams can deliver value more frequently and efficiently.
The Evolution of Programming Languages: From Assembly to AI
Programming languages have undergone a remarkable transformation over the years, progressing from low-level directives to sophisticated tools capable of driving artificial intelligence. Early developers worked with assembly language, a tedious method requiring precise specification of machine actions.
This resulted in higher-level languages like FORTRAN and COBOL, which offered greater abstraction. The advent of object-oriented programming introduced concepts like here modules, further streamlining code organization and repurposing.
Modern languages, such as Python and Java, are highly versatile, supporting a wide range of applications from web development to data science.
The horizon of programming languages is increasingly influenced by the rise of AI. Languages like Lisp and Prolog have long been used in AI research, and new paradigms are appearing that leverage the power of machine learning for code synthesis.
This persistent evolution is poised to transform the way we build software, blurring the lines between human and machine cognition.
Unveiling the Power of Open Source Software
Open source software disrupted the tech landscape by providing a collaborative and innovative platform for developers worldwide. With its origins in community-driven development, open source empowers individuals and organizations to leverage cutting-edge technology without financial barriers. From platforms to infrastructure tools, open source offers a vast community of solutions that cater diverse needs. By embracing open source, we promote collaboration, innovation, and the free exchange of knowledge, ultimately driving technological progress for the benefit of all.
Harnessing the Cloud: A Guide to Software Deployment
Deploying software to the cloud has become an increasingly popular choice for companies. This method offers a range of benefits, including scalability, flexibility, and cost-effectiveness. However, navigating the complexities of cloud deployment can be tricky for teams.
A well-structured implementation involves several key steps. First, one must essential to select the appropriate cloud platform that satisfies your specific requirements. Elements such as cost, performance, and security should be carefully considered. Once the platform is selected, you can initiate the process of configuring your cloud infrastructure. This usually encompasses creating virtual machines, connectivity, and storage capabilities
- After the configuration phase, you can move forward to transferring your software application. This may involve using serverless functions, depending on the nature of your application.
- Testing is a crucial step to ensure that your application performs as expected in the cloud context.
- In conclusion, you should monitor your application's performance and utilize cloud-based monitoring tools to detect any potential issues or areas for optimization.
Demystifying Cybersecurity: Protecting Your Software Assets
In today's digital landscape, cybersecurity is paramount for safeguarding valuable software assets. Security breaches pose a constant threat, aiming to compromise sensitive data, disrupt operations, and inflict financial damage. Safeguarding your software assets requires a multi-layered approach that encompasses robust security measures, vigilant monitoring, and continuous improvement.
- Implement strong authentication mechanisms to prevent unauthorized access.
- Conduct regular vulnerability assessments to identify weaknesses in your software.
- Utilize firewalls and intrusion detection systems to monitor network traffic for suspicious activity.
- Empower your employees on cybersecurity best practices to minimize the risk of human error.
By implementing these strategies, organizations can effectively minimize the risk of cyber threats and protect their valuable software assets.
Developing Intuitive User Interfaces: The Art and Science of UX Design
Intuitive user interfaces are the cornerstone of a successful digital experience. Achieving this level of intuitiveness necessitates a combination of both creative artistry and analytical design principles. UX designers need to endeavor to understand user behavior, processing patterns, and technological constraints to forge interfaces that effortlessly guide users through their engagements.
A key element of intuitive UX design is accessibility. Designers need to make certain that interfaces are available to a varied range of users, no matter their abilities or online literacy.
- Successful intuitive interfaces harness clear and concise language, intuitive navigation, and aesthetically pleasing design elements.
- Moreover, they offer informative feedback to users, elucidating their actions and guiding them toward their objectives.
Finally, the goal of building intuitive user interfaces is to create a seamless and pleasant user interaction. By implementing the principles of UX design, developers can reshape digital products into accessible tools that assist users to achieve their targets with ease.
 Mr. T Then & Now!
Mr. T Then & Now!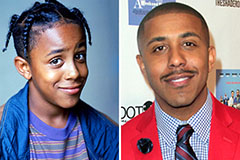 Marques Houston Then & Now!
Marques Houston Then & Now! Freddie Prinze Jr. Then & Now!
Freddie Prinze Jr. Then & Now! James Van Der Beek Then & Now!
James Van Der Beek Then & Now! Bernadette Peters Then & Now!
Bernadette Peters Then & Now!